L2TP/IPSec VPN server
In Keenetic routers, it is possible to set up an L2TP over IPSec VPN server (L2TP/IPSec) to access home network resources.
In such a tunnel, you can absolutely not worry about the confidentiality of IP telephony or video surveillance streams. L2TP/IPSec provides completely secure access to your home network from a smartphone, tablet or computer with minimal configuration: Android, iOS and Windows have a convenient built-in client for this type of VPN. In addition, many Keenetic models offer hardware acceleration of data transfer over L2TP over IPsec.
Importante
A Keenetic device that hosts the IPsec VPN server must be connected to the Internet with a global (public) IP address, and if using the KeenDNS domain name, it must be configured in the Direct Access mode. If any of these conditions are not met, it will not be possible to connect to such a server from the Internet.
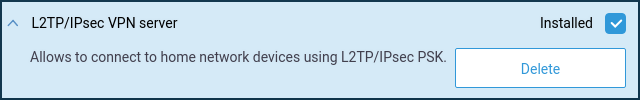
To set up the server, it is necessary to install the system component 'L2TP/IPsec VPN server'. You can do it on the 'General system settings' page in the 'Updates and component options' section by clicking on the 'Component options'.
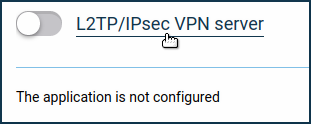
Then go to the 'Applications' page. Here you will see the 'L2TP/IPsec VPN server' panel. Click the 'L2TP/IPsec VPN server' link.
In the 'L2TP/IPsec VPN server' window that appears, specify the security key in the 'Shared IPsec key' field. This security key will need to be specified on the client when configuring the VPN connection.
Importante
This key is also used by the IPsec VPN server (Virtual IP).
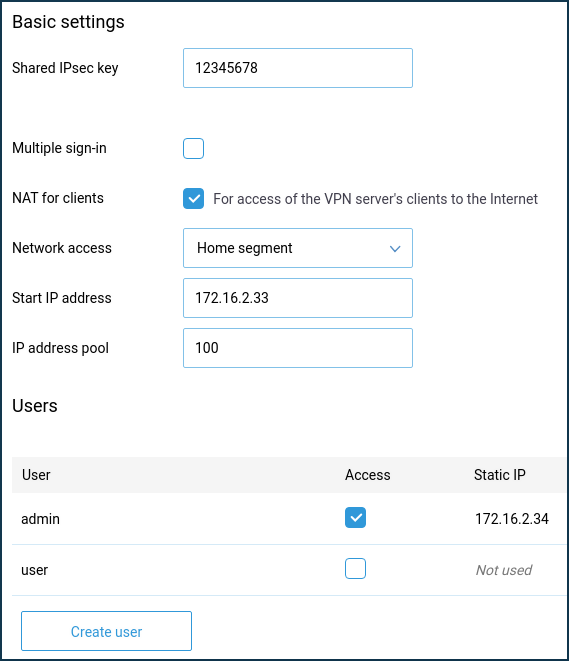
The 'Multiple sign-in' parameter controls the ability to establish several simultaneous connections to the server using the same credentials. This is not a recommended scenario due to the lower security level and the disadvantages in monitoring. However, during the initial configuration, or in cases where you want to allow the installation of a tunnel from multiple devices of the same user, you can leave the option enabled.
Importante
If the 'Multiple sign-in' option is disabled, you can assign a static IP address to the L2TP/IPsec client. This can be done on the L2TP/IPsec VPN server configuration page in the 'Users' section.
By default, the 'NAT for clients' option is enabled in the server configuration. This setting is used to allow VPN server clients to access the Internet. In a built-in Windows client, this feature is enabled by default, and when a tunnel is established, requests to the Internet will be sent through it.
Importante
If you disable the 'NAT for clients' function on the server but do not reconfigure the default routing policy in the Windows client, the Internet access may not work after the installation of the tunnel on the computer.
In server settings in the 'Network access' field, you can also specify a segment different from the Home segment, if necessary. In this case, the network of the specified segment will be available through the tunnel.
The total number of possible simultaneous connections depends on the IP address pool size setting. As with the starting IP address, it is not recommended to change this setting unnecessarily.
Importante
If the 'Start IP address' falls within the network range of the segment specified in the 'Network Access' field, the ARP-Proxy function is enabled to allow access to such VPN client from the specified local segment.
For example, if the home network 192.168.1.0 with a netmask of 255.255.255.0 and the DHCP server setting of 'Start Pool Address': 192.168.1.33, 'IP address pool': 120 is selected, you can set the 'Start IP address' of the VPN server to 192.168.1.154, which falls in the range 192.168.1.1 ~ 192.168.1.254, and have access from the home network to the VPN clients in the same way as access to the local devices.
In the 'Users' section, select the users you want to allow access to the L2TP/IPsec server and the local network. Here you can also add a new user by specifying a username and password.
After configuring the server, set the switch to the 'Enabled' state.
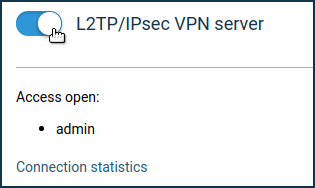
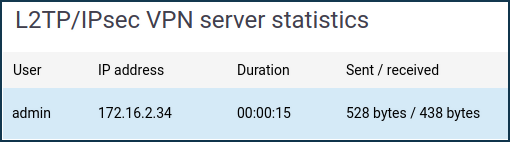
By clicking on the 'Connection statistics' link, you can see the connection status and additional information about active sessions.
If you want to provide clients with access not only to the local network of the VPN server but also in the opposite direction, i.e. from the network of the VPN server to the remote network of the VPN client, to provide data exchange between the two sides of the VPN-tunnel, refer to the Routing networks through VPN instruction.
Nota
To connect to the server as a client, you can use:
A Keenetic router — L2TP/IPsec (L2TP over IPsec) client;
A Windows 10 computer — Connecting to the built-in L2TP/IPSec VPN server from a device on iOS and Windows;
A Windows 7 computer — Example of L2TP/IPsec connection in Windows 7;
An Android mobile device — Connecting to an L2TP/IPSec VPN server from Android;
An iOS mobile device — Connecting to an L2TP/IPSec VPN server from iOS.