To protect your home network from attacks and intrusions from the Internet, Keenetic routers have a firewall active by default.
In most cases, the default settings are sufficient for safety, and no additional firewall configuration is required. But if it is necessary for any specific tasks, Keenetic provides flexible options for security settings to allow or deny access to specific hosts or network services.
Important
By default, your home network is protected from external attacks, and access to the router's management (web interface) is blocked from the Internet.
The firewall can be seen as a set of pre-configured and user-defined filters, with rules set by a user having a higher priority.
Firewall rules are executed in the order they are specified in the list: the top one is the first and then down the list. For any rule, the interface (connection) on which it will be executed must be defined.
In each rule, there must be specified:
A traffic source network and its destination (IP addresses of hosts or subnets);
A protocol for which the rule will work (TCP, UDP, ICMP, etc.);
A port number must be specified for TCP and UDP protocols;
An action to take on a packet: Deny or Allow.
Important
In Keenetic routers, firewall rules are processed after network address translation (NAT) rules. Therefore, when creating firewall rules, you should specify the host's IP address after the address translation.
Keenetic's web configurator offers the most convenient way to manage firewall rules.
Important
Rules created through the web configurator apply only to incoming traffic of the public (WAN) or local (LAN) interface.
It is possible to create rules for any direction through the command-line interface (CLI) of the router.
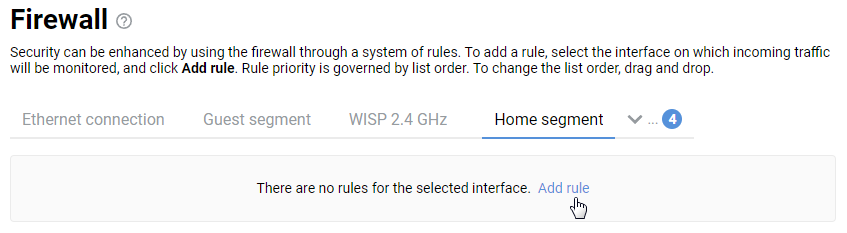
Setting up firewall rules is done on the 'Firewall' page.
To add a firewall rule, select the interface where incoming traffic will be tracked from the list and click 'Add rule'. The rules apply in the order they are located in the list. To change the order of the rules, drag and drop the rows in the table.
Important
Rules should be created for the interface where the filtered traffic is inbound (initiating the session).
In the 'Firewall Rule' window that appears, select an action to be performed for incoming packets and specify conditions under which the action should be performed. In our example, for the 'Home segment' interface, we'll create a 'Deny' rule where we'll specify the source IP address (the IP address of the computer whose access will be denied). As a result, this rule will block access to the Internet only for one host on the local network with the IP address 192.168.1.35.
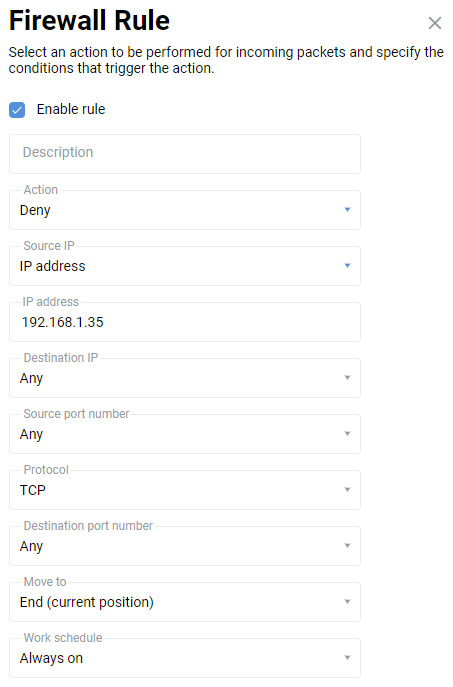
In the 'Action' field, select the action - 'Permit' traffic or 'Deny', and then specify the criteria and conditions coinciding with which these actions will be performed.
In the 'Work schedule' field, you can add a schedule, according to which this rule will work.
Important
When creating blocking rules, the allowing rules must be placed above the prohibiting ones.
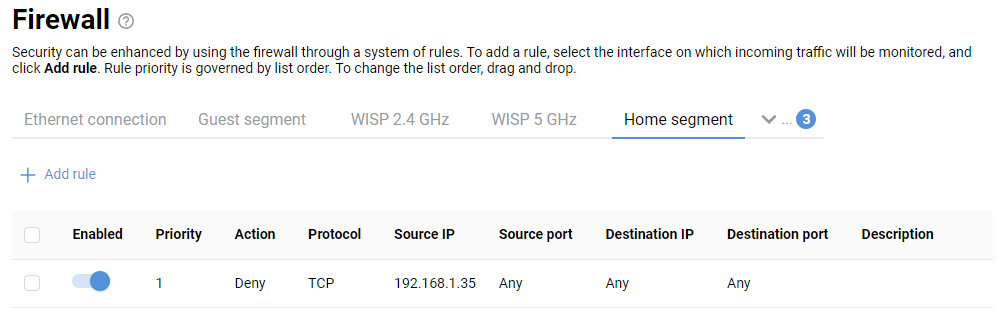
In our example, the following 'Deny' rule was created for the Home segment interface:
Tip
We recommend that you read the instructions:
Starting from KeeneticOS
2.14, the web configurator has implemented group copying, moving and deleting of firewall rules: Copying, moving and deleting multiple firewall rules